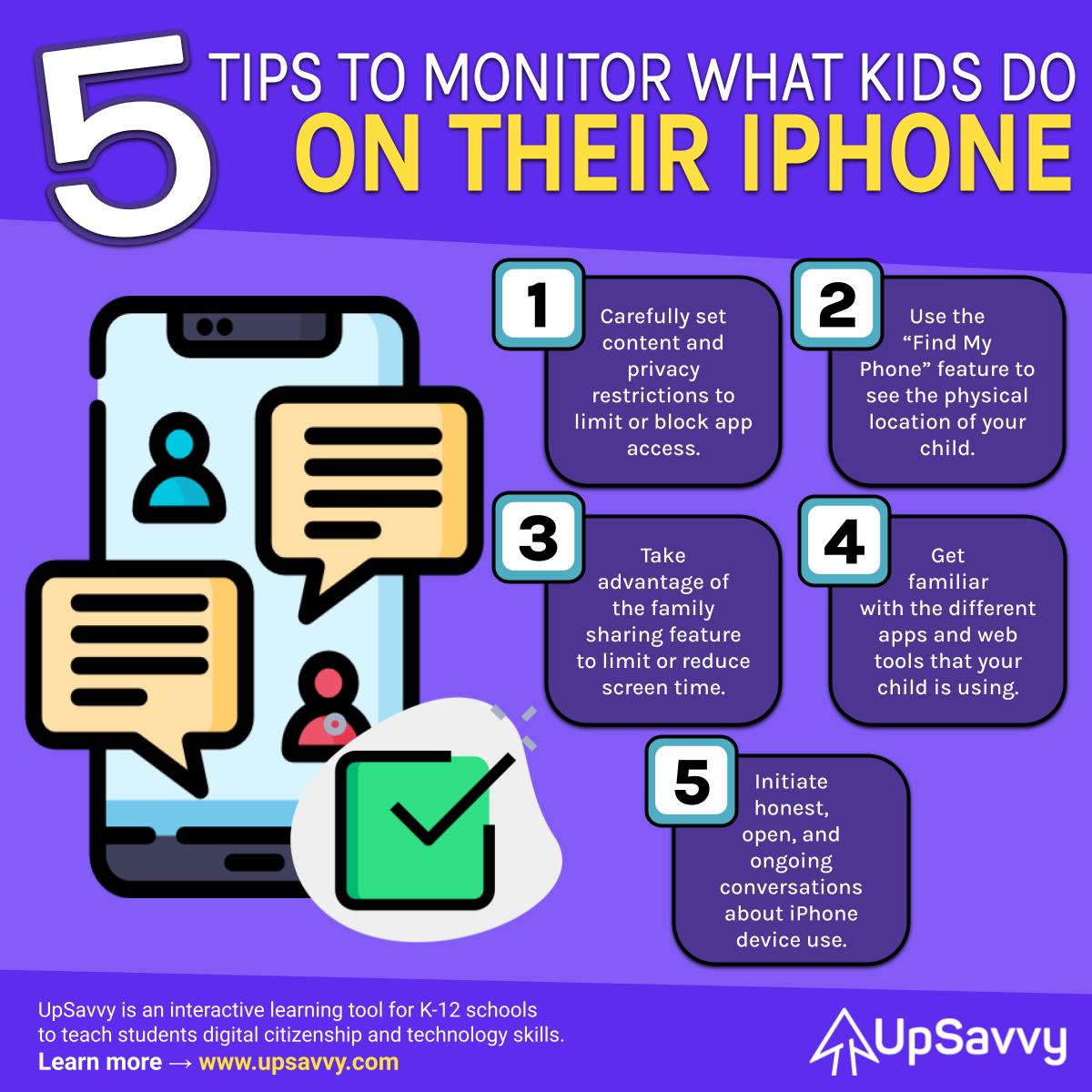
Content & Privacy Restrictions
All iPhones have a great built in feature under settings that allows you to adjust the content and privacy restrictions for the device user. You can set time limits for apps, select which apps are allowed, and even block inappropriate content. This is a great place to start when you want to be able maintain device control and monitor what applications are being utilized.
Find My iPhone
The Find my Iphone feature can be helpful in tracking down a misplaced or lost device, but it also can be an effective validation tool to confirm the physical location of the device user. This can come in handy when confirming the safety and well being of your child, as well ensuring and maintaining trust between parent and child. The physical location of a device should always line up the information that has been communicated in conversations.
Family Sharing
The family sharing feature is available under the settings icon on an iphone and allows family members to share Apple services like iCloud, Apple Music, and Apple TV. Family sharing will allow you to control what content is being used between members and the ability to monitor what is being watched, listened to, and purchased. Family sharing is an effective way to set some parameters around device content and what your child has access to.
Get Familiar
In order to effectively monitor what your child does on your iPhone you should get familiar with the apps and digital tools that they are wanting to use. Understanding how a particular application works, or its purpose, is half the battle of being able to monitor iPhone use. Be sure to know if an app is a game, a communication tool, a school based tool, or a social media platform. Perhaps even conduct a quick Google search to get a brief snapshot of a particular digital app or tool ahead of time to ensure that it is within your comfort zone.
Open Conversations
Always make time for honest, open, and ongoing conversations when it comes to managing and monitoring a powerful digital tool such as an iPhone. Personal responsibility and accountability with a device comes from repeated conversations, building a knowledge base, and establishing trust. Don’t be afraid to have difficult conversations and discuss ways in which device use will be consistently monitored.